In addition to core activities of co-ordinating response to computer and network security incidents and mitigating threats to the infrastructure, the EGI CSIRT team, in collaboration with partners, provides services for security monitoring, security training and best practice dissemination. Find out more about EGI CSIRT’s activities below.
- Incident response: day-to-day security operations are handled by the Incident Response Task Force (IRTF), a small team of security experts distributed over several countries and multiple organizations who, taking part in an on-duty rota, act as first responders to reports of security incidents within the EGI Infrastructure. If required, security forensics expertise within the IRTF is made available to sites for the investigation and resolution of incidents.
To report an incident follow the SEC01 procedure and inform the local security team, NGI security officer and EGI CSIRT.
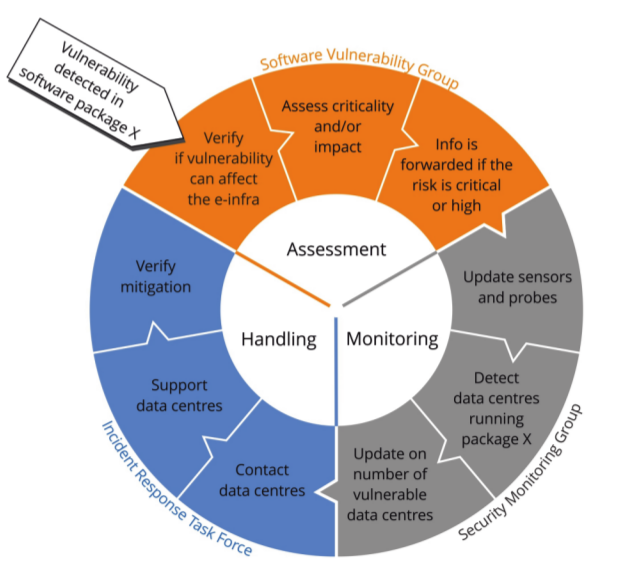
- Security monitoring: In order to obtain information about the state of the infrastructure and enable a pro-active security stance, the EGI CSIRT uses a security monitoring framework that collects and evaluates data from all EGI sites. This framework enables the EGI CSIRT to check basic security characteristics of the services that EGI sites make available to its users, including services’ software patching levels and deployed mitigations.
The EGI CSIRT deploys a security monitoring framework to collect and evaluate data from all EGI sites. We use Pakiti, Pakiti2, Security Dashboard
- Security policy and procedures: Operational security can only be organized within a proper policy framework, regulating access to, provision and usage of the infrastructure. EGI CSIRT actively participates in the development and maintenance of the policy framework to ensure it remains relevant in an evolving infrastructure.
- Software vulnerability advisories: EGI CSIRT members participate in the EGI Software Vulnerability Group (SVG) which acts is to minimize the risk to the EGI infrastructure arising from software vulnerabilities. Handling vulnerabilities is an important part of incident prevention and, when vulnerabilities are reported, the SVG issues advisories for sites including information on risk level and, where possible, mitigating actions. For critical risk vulnerabilities the EGI CSIRT operates procedures to ensure that all EGI services take appropriate action to eliminate or mitigate the risk to the infrastructure.
To report a software vulnerability, send and email to report-vulnerability@egi.eu
- Training: EGI CSIRT organizes training events for sysadmins focused on forensics, incident prevention and incident response. EGI CSIRT has developed and offered material in the three categories of defensive, offensive and role-play training. We will anounce the upcoming trainings in advance.
All EGI-CSIRT activities are part of the EGI Security Coordination service, which is part of the EGI Service Catalogue.